Damn Vulnerable Hybrid Mobile App (DVHMA)
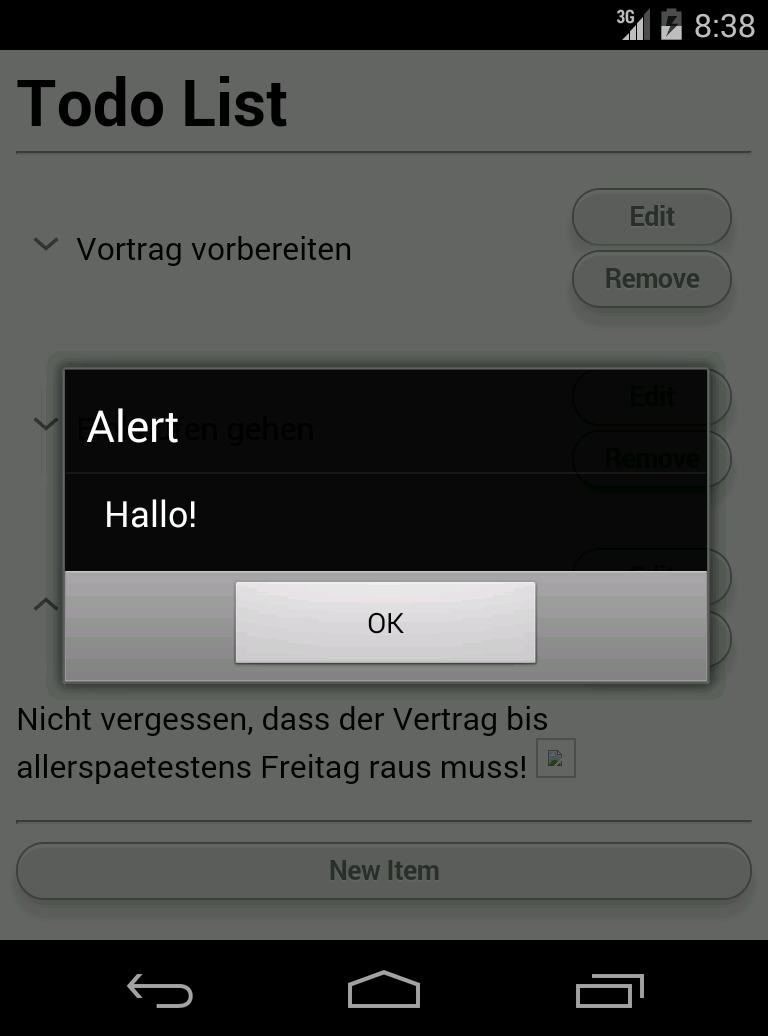
Last month, we got interviewed by Hakin9 about one of our “side-projects”: DVHMA - The Damn Vulnerable Hybrid Mobile App. DVHMA is a hybrid mobile app (for Android) that intentionally contains vulnerabilities. Its purpose is to enable security professionals to test their tools and techniques legally, help developers better understand the common pitfalls in developing hybrid mobile apps securely.
We developed it to study pitfalls in developing hybrid apps, e.g., using Apache Cordova or SAP Kapsel, securely. Originally we developed DVHMA as a test case for evaluating static application security testing tools [1]. Hence, the focus was to develop a deeper understanding of injection vulnerabilities that exploit the JavaScript to Java bridge.
Today, DVHMA is becoming increasingly popular by penetration testers and forensics experts that want to learn the specifics of Cordova apps.
DVHMA is published under the Apache 2.0 License and you are welcome to participate in its further development. We are currently working on improving DVHMA and hope to be able to release a substantial update in the future.


