


Theorem-prover based testing combines testing and verification: tests are derived from a formal specification (or model, i.e., it is a model-based testing technique) proof techniques. HOL-TestGen is a theorem-prover based testing environment on top of Isabelle.
HOL-TestGen: a theorem-prover based testing environment
The main result of our work in the area of theorem-prover based testing [1] is the HOL-TestGen [2] system. HOL-TestGen is jointly developed by the Software Assurance & Security Research Team at the University of Exeter, UK and the Verified Algorithms, Languages and Systems team at the LRI (CNRS and University of Paris-Sud), France.
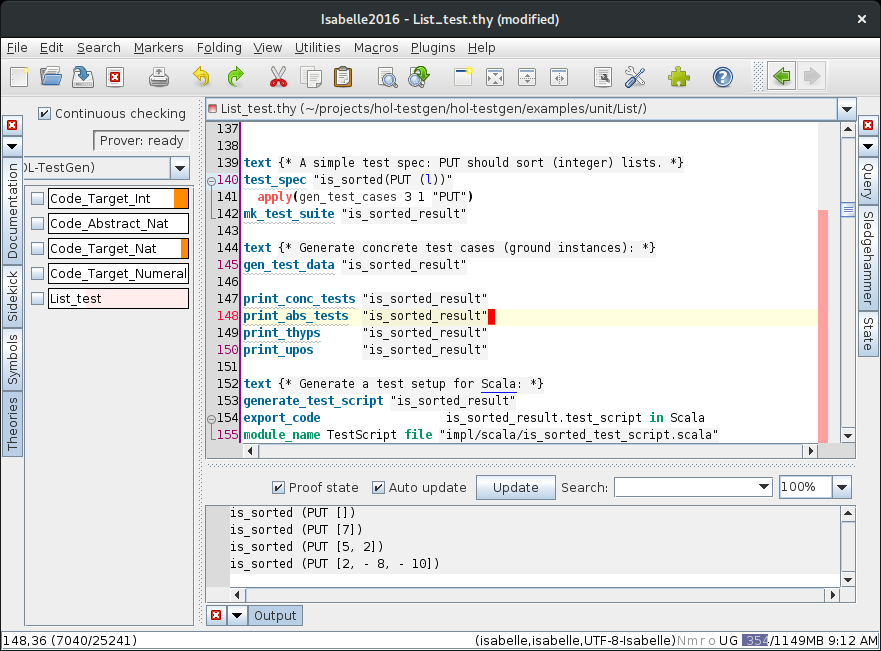
As a unique feature, HOL-TestGen supports the end-to-end life-cycle of formal system testing and verification: from a formal specification that can be formally verified, to formally verified specification transformation (model-transformation), to abstract test case generation, concrete test data generation, to the generation and execution of test scrips that test a real system under test.
HOL-TestGen has been used in large case studies in various application domains, including conformance testing of security properties (e.g., firewall policies [3] and health-care-specific access control systems [4]).
HOL-TestGen is free software; you can redistribute it and/or modify it under the terms of a BSD-style license.